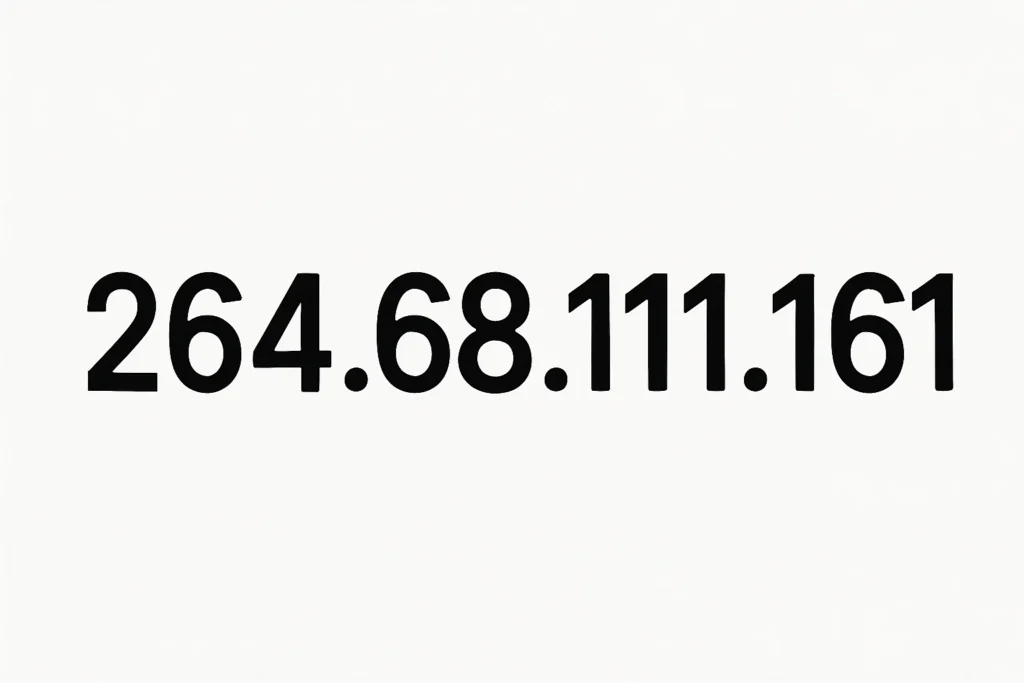
1. Introduction to 264-68-111-161
IP addresses are fundamental to the digital world, serving as unique numerical identifiers for devices connected to a network. Each device, from a personal computer to a server, requires an IP address to communicate effectively across networks and the internet. The IP address 264-68-111-161 stands out because it is an invalid IP, exceeding the numerical limits allowed in IPv4. While it may appear in network logs, documentation examples, or test environments, understanding its implications is crucial for professionals in network troubleshooting and cybersecurity. This article explores the structure, potential risks, validation techniques, and best practices related to 264-68-111-161 and similar invalid addresses.
2. What is an IP Address?
An IP address is a unique identifier used to route packets across networks. IP addresses come in two main forms, IPv4 and IPv6. IPv4 addresses consist of four octets separated by dots, a format known as dotted decimal notation, while IPv6 uses hexadecimal segments separated by colons. IP addresses are essential for network communication, enabling devices to send and receive data accurately. Each octet in an IPv4 address ranges from 0 to 255. IP addresses can be public, allowing devices to communicate over the internet, or private, restricted to internal networks. Proper configuration ensures data transmission efficiency and minimizes system errors or misconfigurations in network routing.
3. Why 264-68-111-161 is Invalid
The IP address 264-68-111-161 is invalid because its first octet, 264, exceeds the maximum allowed value of 255. Such invalid IPs often occur due to human errors, typos, or misconfigured software. If used in live networks, these addresses can lead to connectivity failures, malformed entries in network logs, or analytics noise in monitoring dashboards. Misconfigured devices may generate error messages or fail to route packets properly, causing delays in communication between servers, routers, and other network devices. Understanding the concept of octet range violations is critical for preventing misinterpretation of invalid addresses and for maintaining overall network integrity.
4. Placeholder and Demo IPs
Invalid IPs like 264-68-111-161 often appear as placeholder IPs in technical documentation, scripts, or tutorials. Developers frequently use these demo IPs in test environments to illustrate network configurations or simulate data transmissions without affecting real systems. These addresses help in teaching IP address structure, address validation techniques, and network troubleshooting scenarios. Placeholder IPs also serve as instructional examples for network administrators, enabling them to understand misconfigurations, simulate routing failures, and perform packet inspections safely. Using such addresses provides educational value while preventing accidental exposure of real network devices.
5. Network and Connectivity Implications
Network devices rely on valid IP addresses to establish connections and transmit data. When an invalid IP like 264-68-111-161 is present, connectivity issues often arise. Routers may reject packets, firewalls may block traffic, and servers may log system errors. These invalid addresses can interfere with normal routing, leading to misconfigured network nodes and erroneous analytics. Network monitoring tools may flag the IP as malformed, and intrusion detection systems might generate false alerts. Understanding the impact of invalid IPs on connectivity helps administrators troubleshoot issues effectively, ensuring reliable data transmission and maintaining cybersecurity best practices across devices and network interfaces.
6. Cybersecurity Risks
Invalid or spoofed IP addresses pose significant cybersecurity risks. Attackers can exploit fake IPs to mask their identity, deliver malware, perform phishing attacks, or manipulate network devices. Security systems often detect unusual IP patterns through intrusion detection and threat intelligence mechanisms. Using invalid IPs in logs or as fake sources in packets may trigger alerts in network monitoring tools. Analysts must differentiate between placeholder or educational IPs and potentially malicious traffic to avoid false positives while maintaining vigilance over network security. Proper monitoring of spoofed traffic and bot activity is crucial for mitigating risks associated with non-existent IPs.
7. Understanding Network Logs
Network logs record detailed information about data transmission, IP tracking, packet flow, and user identity. Invalid IPs like 264-68-111-161 often appear in these logs due to human errors, automated testing scripts, or misconfigured software. These malformed entries can cause server log confusion or create analytics noise that obscures actual threats. Effective log analysis enables cybersecurity professionals to filter placeholder IPs from real incidents, improving data quality and reducing false alarms. Proper interpretation of network logs is essential for threat analysis, intrusion detection, and maintaining accurate records of device connectivity and traffic routing.
8. Tools for IP Validation
IP validation ensures that an address complies with IPv4 format rules and falls within the allowed octet range. Professionals utilize various tools, including IP lookup services, command-line tools, traceroute tests, ping requests, and WHOIS lookups. These tools provide information about ownership, geolocation, and network reachability. Validation prevents configuration errors, routing failures, and network disruptions caused by invalid entries. Regular verification of IP addresses enhances cybersecurity, improves connectivity, and ensures proper functioning of servers, routers, and other network devices across both private and public ranges.
9. Address Ranges and Standards
IPv4 addresses are divided into public and private ranges, with specific octet limits. Private IP ranges, including 10.x.x.x, 172.16.x.x, and 192.168.x.x, are reserved for internal networks, while public ranges are assigned for internet-facing devices. Addresses exceeding octet ranges, like 264-68-111-161, are invalid and cannot be routed effectively. Understanding IP range standards allows network administrators to allocate addresses correctly, prevent conflicts, and maintain compliance with cybersecurity best practices. Address breakdown and semantic validation of IPs are essential for identifying non-routable or misconfigured addresses.
10. Common Problems with Misconfigured IPs
Misconfigured software or devices can generate invalid entries that disrupt normal operations. Malformed addresses, automation errors, or typos can lead to packet loss, server log confusion, device connectivity failures, and traffic routing problems. Misinterpretation of these entries may trigger unnecessary alerts or hinder network troubleshooting. Network administrators must identify configuration errors and perform input validation to prevent system errors. Proper documentation, instructional examples, and simulation scenarios help mitigate risks associated with invalid IPs, ensuring reliable operation of network interfaces, routing devices, and monitoring tools.
11. Best Practices for Network Administrators
Network administrators should adopt comprehensive practices to handle invalid or unusual IPs. Conducting IP validation before deployment ensures that addresses conform to IPv4 format rules. Using reserved address ranges for testing reduces risks to production networks. Monitoring network devices with analytics dashboards and network monitoring tools allows early detection of malformed or spoofed IPs. Configuring firewalls and routing rules properly prevents unauthorized access, mitigates cybersecurity threats, and ensures smooth connectivity. These practices support overall network security, accurate log analysis, and reliable data transmission across servers, routers, and client devices.
12. Educational and Simulation Use Cases
Invalid IPs serve as valuable tools for teaching IP structure, address validation, and troubleshooting techniques. Educational use cases include demonstration scenarios, simulation exercises, and instructional examples for both IPv4 and IPv6. Test data and placeholder IPs allow students or junior administrators to practice network configurations, monitor packet flow, and analyze analytics dashboards without affecting live systems. Simulation scenarios can replicate routing failures, firewall restrictions, and connectivity errors safely, providing hands-on experience in network troubleshooting, semantic validation, and cybersecurity analysis.
13. Advanced Troubleshooting Techniques
Advanced troubleshooting involves analyzing packet flow, performing traceroute and ping tests, and reviewing network logs for anomalies. Invalid IPs like 264-68-111-161 may indicate misconfigured software, human errors, or automated testing scripts. Combining network monitoring tools with technical documentation helps identify underlying causes. Analysts can examine traffic routing, perform input validation, and inspect packet data to pinpoint connectivity issues. Simulation scenarios, instructional examples, and developer tutorials provide additional insights into addressing errors while maintaining proper network device configuration and security protocols.
14. Security Analysis and Threat Intelligence
Studying invalid IPs supports threat intelligence, security analysis, and bot activity monitoring. Spoofed traffic, phishing attempts, and malware distribution are often linked to fake or non-existent IPs. Intrusion detection systems and firewalls analyze traffic patterns, log anomalies, and suspicious entries to detect threats. Effective cybersecurity practices require differentiating placeholder or demo IPs from malicious activity. By combining analytics dashboards, IP tracking, and packet inspection, cybersecurity professionals can mitigate risks while maintaining compliance with IP range standards and network security policies.
15. Conclusion
The IP 264-68-111-161 demonstrates the importance of IP validation, proper network configuration, and cybersecurity awareness. While placeholder IPs serve instructional purposes, invalid addresses in production networks can lead to system errors, connectivity issues, and cybersecurity threats. Understanding address structure, octet ranges, and network standards is crucial for administrators and professionals. Regular validation, monitoring, and simulation exercises reduce errors, improve routing efficiency, and maintain secure and reliable network communication. Proactive management of IP addresses ensures data integrity, threat mitigation, and seamless connectivity across all devices.
FAQs
Q1: Why is 264-68-111-161 considered invalid?
It exceeds the allowed octet range of 0–255 for IPv4 addresses and cannot be routed properly.
Q2: Can invalid IPs be safely used in test environments?
Yes, they can act as placeholder IPs for simulations, educational purposes, or instructional examples without affecting live networks.
Q3: How do you validate an IP address?
Use IP lookup tools, traceroute tests, ping requests, WHOIS lookups, and command-line validation to check structure, range, and routability.
Q4: Are fake or spoofed IPs dangerous?
Yes, they can be used to conceal identity, deliver malware, execute phishing attacks, or interfere with network security monitoring.
Q5: What are the best practices for managing invalid IPs?
Perform regular IP validation, use reserved ranges for testing, monitor networks with analytics dashboards, configure firewalls, and ensure proper routing.